Quick note: if you’re viewing this via email, come to the site for better viewing. Enjoy!

Photo by Thirdman, please support by following @pexel.com
So you’re sat at your computer and it’s time to look and evaluate how your OnlyFans account has been doing but you dread the thought of having to log in, and crunch numbers, and the overshadowing thought of having to brainstorm new ideas begin to make you gag because… well frankly, you don’t like having to worry about this additional work on top of what you’re already managing.
You figure this would be better suited for a group who had a knack for handling this much information and coming up with possibilities for you to gloss over.
If you could find and hire a team like that would see yourself being the big boss and could even, make your life slightly easier and slightly less shameful.
Now the only thing is to find this special group to crunch your numbers so you can get to sleep at night. Sorry mom.

Photo by Anna Nekrashevich, please support by following @pexel.com
Dumpster Diving Data
Who are these mad people who rummage through data like a crackhead rummaging through your trash in hopes to find anything that’s going to help them score some…well crack?
Look no further than Data Analyst. Creative name, again I know but Linda listen. Data Analyst is professionals who retrieve, organize, and analyzes information from various sources to help an organization achieve business goals.
They often use logic, statistical techniques, and computer programming to turn numbers into information that an organization can use to improve workflow and business processes. So if you ever wondered why your job strangely and suddenly came up with more tasks for you to do at work, yeah, it’s safe to assume these guys were the culprit.
An important goal of the analysis is to distinguish between what data is important and what data should be given less weight. They do this by using data analysis to produce accessible graph charts, tables, and reports.
This is information that’s exciting for them but boring to the average person who wants to upload a twerk video online. In any organization, data analysts are also responsible for data quality and preparing reports for internal and external stakeholders.
You can picture them being the boogeymen you would hide from when you’re having a bad third quarter and you don’t want to hear about how much your company is failing at it.
They’re a real “in your facts, not your feelings” type of people.

Photo by Karolina Grabowska, please support by following @pexel.com
Data Shakes
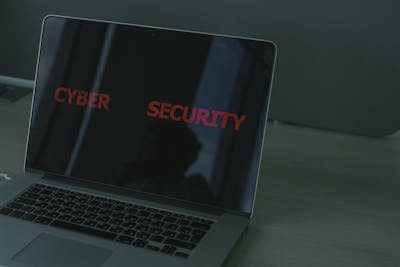
Do you want to know who in their right mind uses these data hounds? Get ready for this tall order, retail banks use data extensively to understand how their customers use their accounts and to help identify security risks. They’re also leveraging big data in location intelligence to determine how to manage their branch locations and set location-based performance goals most efficiently.
Farmers, not being the first people on your list that would use data analysis, are now using them for agriculture and they are posed to grow only more important as predicting the weather and squeezing maximum productivity out of the land. This wouldn’t be so much of a problem if Earth wasn’t trying to heal itself due to the need of feeding a growing population of humans.
Real estate firms and this is no surprise here, leverage big data for better property analysis, better trend analysis, and a better understanding of their customers and markets.
Data has long been crucial for doctors seeking to figure out, based on analysis of a larger number of data points collected from many patients, examples are findings in which blood pressure range is normal or how much sugar you should consume each day.
Now the healthcare industry is using data analytics to answer bigger, more complex questions. Like seeing how much they could charge you for treatment, I say you because insurance companies ensure they don’t pay all of the cost.

Photo by Anna Shvets, please support by following @pexel.com
Data Diagnosis
These data-horny-driven people, how important are they? Well, they can help an organization understand risk and take preventive measures if the organization chooses to listen.
As a result, data analysis helps companies make informed decisions, create a more effective marketing strategy, improve customer experience, and streamline operations, and that’s among many other things.
All of these are excuses used to squeeze that sweet work juice from employees in the name of performing what’s called “improvements”.
Implementing data analysis into business models means companies can help reduce costs by identifying more efficient ways of doing business and by storing large amounts of data.
Side effects of reducing cost are but are not limited to, getting rid of your favorite coffee machine in the office, moving Taco Tuesday to Wednesday, lack of proper working equipment or equipment, and can even cause job loss via company downsizing.
So yeah, these data fiends have a massive play and a mass amount of uses. Again, everything is data and it’s everywhere, so these people are always turned on.

Photo by Andrea Piaccquadio, please support by following @pexel.com
Only Data Abound Fans
You may be thinking “why would I hire someone to do all of this, I get aroused at the thought of crunching numbers. I could give this a shot. Do I need a degree?”
Here’s a degree not needed inbound however, you are going to need a structured and formal approach to learning the necessary skills. The best way to do so is through a project-based course. Data analysis is also not required to have advanced coding skills.
Instead, they should have experience using analytics software, data visualization software, and data management programs. Data analysts are required to have a strong grounding in mathematics to succeed.
Again, if you’re an advent reader of mine, you already know Z-Daddy is out. Computers do the math for me, that’s how it’s always been. Reviewing and if necessary, improving your math skills may be needed before learning to become a data analyst.
The field of data science is fast-paced, demanding, and challenging. Learning to perform your responsibilities correctly can take some time too and that can add to your stress.
However, keep in mind, you’re not a machine and that working is important but it’s not worth sacrificing your health, then again, no job is.

Photo by Antoni Shkraba, please support by following @pexel.com
Made it this far and found this to be entertaining? Then a big thanks to you and please show your support by cracking a like, scripting a comment, or plug-in to follow.
Would like to give sincere thanks to current followers and subscribers, your support and actions mean a lot and has a play in the creation of each script.
Think you have what it takes to become a Data Analysis?
Script a comment about what domain knowledge you’re interested.