Quick note: if you’re viewing this via email, come to the site for better viewing. Enjoy!
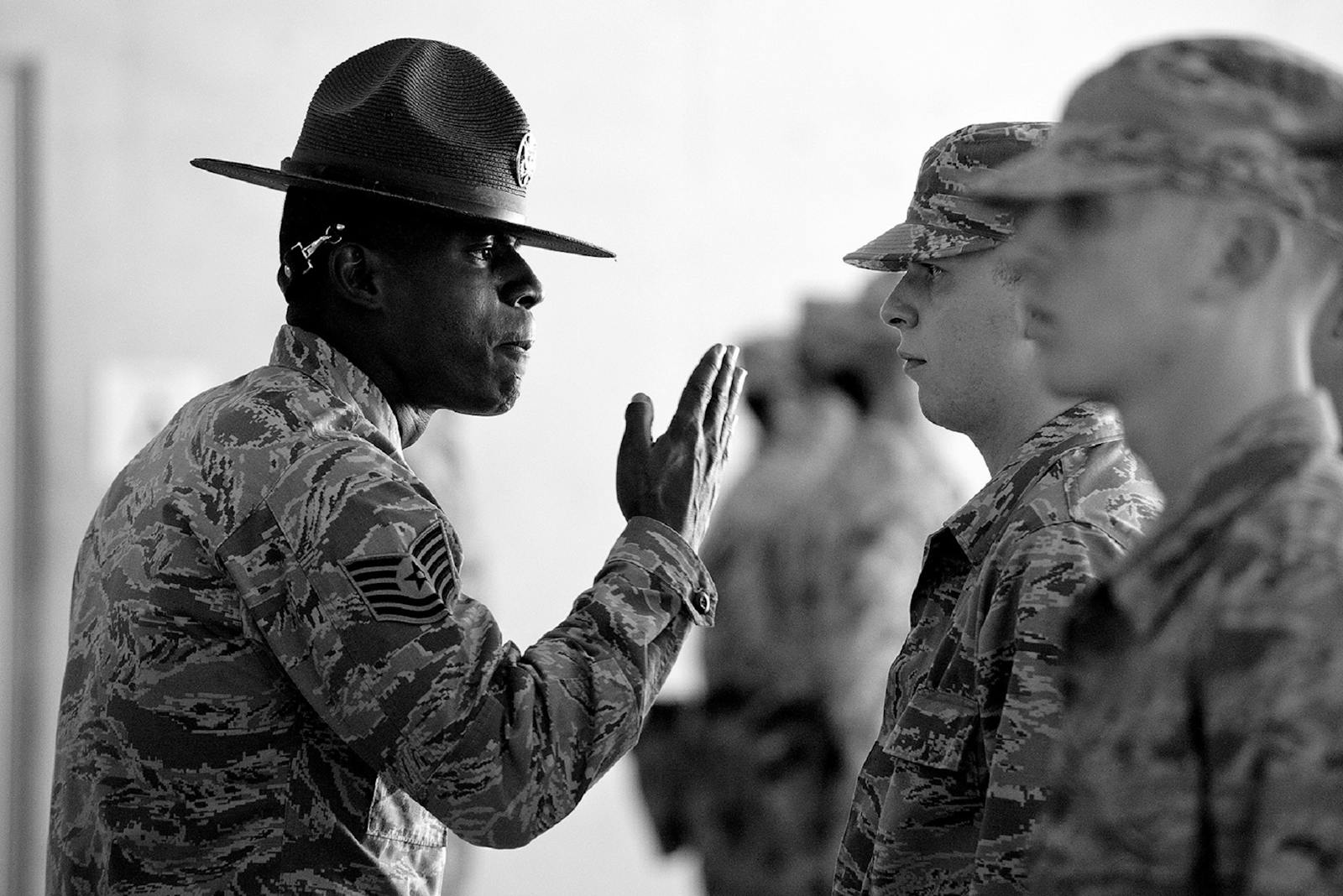
Photo by Pixabay, please support by following @pexel.com
It’s crunch time, you’re sitting at your computer with your shoulders slumped down heavily, your face in your hands covering up your exhaustion. You rest your head back in search of relief due to the increasing weight of your thoughts.
Thoughts flanking your left and right rapidly firing questions of how you are going to fend off bills, provide for yourself and your family (if you have one), and see yourself in a better position than you currently are.
You ask yourself; “How would I be able to get to the next level?” You have made your declaration and have made it known that you don’t want to spend your best years in school, trying to ascend your way to the top of the class because let’s be honest, going to school has never been your kind of jam.
You were more of a System of a Down kind of person in your glory days and going to school would see your dreams end in Chop Suey. Would you be interested if you found out there was another path you could take?
You just might have to strap up your bootlaces and camp it out a bit.

Photo by Christina Morillo, please support by following @pexel.com
The New About Face
With not wanting to be Another Brick in the wall, what is going to see you get to the next level? Simple, you can just join the Army and become more meat for the machine instead.
No, you don’t have to join the Army, you can opt for the less painful version which is a coding boot camp. Coding boot camps are short-term intensive training programs that provide students with practical and job-ready technical skills.
Boot camps enable students to go from “drooling at the mouth I can’t read, nor can I feel my brain” to “it’s so easy a caveman can do it.” Shout out to my Geico OGs. This provides students with the confidence and knowledge needed to immediately apply their new skills to solve real-world problems, please keep in mind solving world hunger and peace will not be included.
Now, undergoing this training looks great on paper but can have a steep learning curve depending on the instructor and class structure. Like the aim of a trade school, a coding boot camp is usually built around building marketable technology skills that can be leveraged toward a lasting career…or until they decide to let you go, I’m not going to lie to you, it’s not all sunshine and rainbows kid.
And with how well-known companies are treating longtime employees like they’re the side-chick in public and acting like they don’t know them nowadays it’s something to brace for. The world will embody you as a stray cat, floor the gas pedal, hear a thud and pretend it never saw you in the rearview mirror.

It might not be sober, but I’m going to make it.
Photo by RODNAE Productions, please support by following @pexel.com
Boot Perfect
So, coding boot camps, who uses them? Well, people who want to be developers obviously. This goes either way since people who are not developers and people who are can both benefit from entering a coding boot camp which either could be attempting to break into the field or simply learn another avenue of IT.
These programs often cover basic programming languages like JavaScript, SQL, and Python, along with modules on current industry software, tools, techniques, and best practices. You know, everything you would get if you enlisted minus being yelled at daily and performing repetitive self-affirmation of “There’s no place like home, there’s no place like home”.
As mentioned earlier, there’s no need for prior coding experience but at the same time having a little experience is a plus. A quick thought let’s say you were homeless and just so happen to have the funds through a Miracle on 31st Street sign yourself up for a coding boot camp, you could theoretically learn the skills needed to land yourself a job. However, these conditions are theoretical and in a perfect world, the odds may be low but they’re still there.
Coding boot camps, like many trade schools, are typically run by private, for-profit companies and is offered both in-person or online depending on the program.

Photo by Pixabay, please support by following @pexel.com
Camp Field of Dreams
Coding boot camps, why are they so important? Well, there’s a massive shortage of skill, and developers are finding that trying to use those good ole job descriptions isn’t the vibe anymore.
To pair with that companies are finding themselves starting to favor the results of over-time-based experience versus simply just attending a four-year college and getting real-world experience later than sooner. This means going out and getting involved in as many hands-on projects as you can versus asking your parents for that sweet financial blood juice called a loan.
Now you may be wondering “Are coding boot camps worth anything?” The short answer is yes. I have checked around a few forums and have seen a few hiring recruiters say that this along with certificates is something they take into consideration.
I have a ton of certificates however, my email inbox is piled with rejection letters and my phone doesn’t even ring (the ringer is on, I checked). Am I saying this for you to feel bad for me? No, but you’re welcome to.
Just know, IT and a few other fields have gray areas, and this is one of them. I will say coding boot camps can work it just depends on your goals and you. That’s rich coming from me, I know but shut up, I’m being positive.

Photo by Maik Kleinert, please support by following @pexel.com
Wrong Boot Size
Wondering if completing a coding boot camp is something you could put on your resume? I will tell you…yes, yes you can, again I’m being positive. Not only does it show you have the needed skills and education, but it also displays that you have the dedication and work ethic to successfully complete a challenging program.
Now, while all of this sounds great, one thing to keep aware of is coding boot camps have some shortcomings such as limited personal instruction, which is depending how big the group you’re a part of, the instructor may not be able to provide enough feedback regarding your query on a project.
This is one of those, sitting with your hand raised high, the teacher selects you, and hears your question but never answers because someone in the class is having an outburst. They don’t mean to ignore you, but thanks to your classmates, it happens.
The other issue to be aware of is the “one size fits all”. Coding boot camps sometimes will have you learn something either you already know, or they think you should, but your skill level isn’t there and this ends up hurting more than helping.
This sucks but being selective with what camps you opt into by using reviews and checking the curriculum could save you from being fitted wrong.

Private: I DID SIR!
Drill Instructor: THEN WHY AREN’T YOU READING MORE SCRIPTS!?
Photo by Pixabay, please support by following @pexel.com
Made it this far and found this to be entertaining? Then a big thanks to you and please show your support by cracking a like, scripting a comment, or plug-in to follow.
Would like to give sincere thanks to current followers and subscribers, your support and actions mean a lot and has a play in the creation of each script.
Thinking about enlisting into a coding boot camp?
Script a comment below about one you’re interested in.












