Consider following on social media!
Quick note: if you’re viewing this via email, come to the site for better viewing. Enjoy!

Sean: I know, I’m reading it… and stop calling him that. That’s weird bro.
Photo by Pixabay, please support by following @pexel.com
Here’s a question for you. Can you recall what you were doing back in your younger days? Like around the age of 15 or maybe even younger, 12. I would assume that for most people, you were either being grounded by your parents (or parent, I understand for some people a single-parent ran household may have been a reality) for something stupid you did or not being grounded and running around outside with your friends.
The point was, you were too busy either with your parents or with your friends to even have the thought of being seated in front of a computer. And in some cases, this shows signs that you grew up with a healthy childhood. But on the other hand, if you were, or tend to be anti-social, then forming together all the hallmark traits of becoming a hacker could have been something on the menu for you. You don’t know what a hacker is? Let me script it for you.
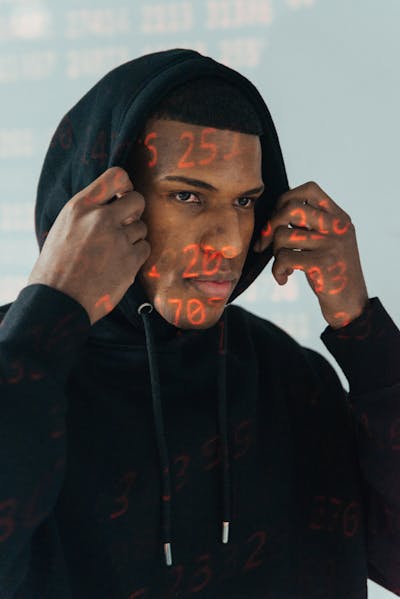
Photo by Mati Mango, please support by following @pexel.com
Hacking Many Hats
Before we start this, I want to be clear, hackers do not sit in front of a computer in the dark typing really fast with a hoodie on trying to crack code…the brightness from the screen tends to hurt our eyes after a while. There are a lot of meanings for the term “hacker”, but the actual definition doesn’t match the sexiness of Hollywood’s definition.
A hacker is someone who uses their skills to gain access to systems and networks without authorization. And before you ask, no, there isn’t an age limit to becoming a hacker. Hackers often fall into one or two of the three categories, you have “Black Hat” – the cybercriminal who is looking to illegally access a system with malicious intent, “White Hat” – the “good guy” who identifies weaknesses in an architecture of an organization which they then inform and advise, and last is “Gray Hat” – which is the combination of both white hat and black hat. Needlessly to say, they operate to what suits their best interest at the given time.
There are other types of a hacker, “Green Hat” – newborn hackers, “Blue Hat” – are white hats who are employed to improve security systems and conduct pen-testing, and the last is “Red Hat” – which are vigilante hackers, these are the individuals that hack in the name of justice.

Photo by Andrea Piacquadio, please support by following @pexel.com
Big Wins with You Losses
Hackers tend to go after big-name financial institutions because of the chance to win big and get a nice payday. However, the risk of doing so results in possibly being caught, fined, and put in prison. So what is a better alternative to avoid that? That’s right, you guessed it, they target the little guy, putting your sweet cornhole on the menu.
While your money may be the most important thing to you, your information like social security, address, and entire name, pretty much everything that says who you are online and in life is way more valuable to a hacker.
The collecting of your personal information is called “information aggregation” and once complete or they feel enough is acquired could result in you getting charged for things you didn’t sign up for, like a loan, a timeshare, or getting a speeding ticket in the mail for a car you don’t own. Basically, your data goes up for sale on the dark web to the highest bidder. And here you were thinking no one had an interest in you, well not you per se since it’s the data they want but still don’t discredit yourself. You go you.
Enjoy the read so far? Why don’t you consider subscribing so you can keep up to date?

Photo by Myicahel Tamburini, please support by following @pexel.com
Hacking When We were Young
Remember when I mentioned that anyone could be a hacker? I was kidding but then again, I wasn’t. You see hackers can come in many shapes, sizes, and flavors. Flavors are the level of skills that they possess to get the job done. Most hackers are often referred to as “Script Kiddies” (No, there’s no relation to them and this site, you’re safe), they’re low-level and mainly purchase malicious code also known as scripts to use to perform malicious attacks.
But then you have your hackers who really know what they’re doing. Such as the likes of Kevin Mitnick- the world’s most famous computer hacker. He hacked into North American Defense Command, Digital Equipment Corporation’s network system. He was arrested and later upon release, decided to hack Pacific Bell’s voicemail system as a flex to show that he could.
Albert Gonzalez started around the age of 12 and was later arrested for debit card fraud in relation to stealing card information. He stole more than 180 million payment card accounts across different companies. And Jonathan James or maybe formally known by his fictitious name “C0mrade”, was deemed one of the best hackers in history.
This was attributed to him gaining access to private network systems with the flex being “this was done just for the fun of it”. Again, recall what you were doing back when you were 15, at the age of 15, he hacked into NASA (National Aeronautics and Space Administration), the Department of Defense (DoD), and South Bell to steal software.
This is insane because his hacking into NASA led to them being shut down for 21 days and cost about $41,000. Getting things fixed was cheaper back in the day, am I right?

Photo by Mati Mango, please support by following @pexel.com
So, you’re probably worried about trying to protect yourself from getting hacked and having all your juicy information all over the internet. Well, I have good news, it’s too late. Well, not entirely, maintaining best practice use of devices and being mindful of your interactions on the internet could save you a lot of financial pain in the long run.
Never leave your device alone in an area whether you trust your surroundings or not, practice using complex passwords – involving letters, numbers, and characters, which makes it harder and takes more time to crack. Do not use any part of your name or the name of anyone you may know for Bluetooth and or Wi-Fi devices as this could give hackers possible information to utilize and further their pursuit.
Always use multi-factor (MFA) or two-factor authentication (2FA) when dealing with online accounts and any other login site as this helps with ensuring that it is you accessing them. Always make use of anti-virus/anti-malware as this will hinder hackers’ attempts to install unwanted programs/files onto your machine. And always make sure your operating system, the OS, is up to date.
Most of how to protect yourself is using common sense, like you wouldn’t just leave your front door unlocked while you’re away on vacation or just have some random person walk in your house to Netflix and chill, don’t leave your device unattended, and don’t let people you don’t know on your device or network. I mean I know hackers can get clever and lucky but most of the time it’s made easy for them.

Photo by Andrea Piacquadio, please support by following @pexel.com
Made it this far and found this to be entertaining? Then a big thanks to you and please show your support by cracking a like, sharing this with whomever, scripting a comment, or plug-in to follow.
Would like to give sincere thanks to current followers and subscribers, your support and actions mean a lot and has a play in the creation of each script.
Do you have a feeling that may have missed something about hackers? Script a comment below.









