Quick note: if you’re viewing this via email, come to the site for better viewing. Enjoy!

Photo by Andrea Piacquadio, please support by following @pexel.com
Let’s start this off by asking a simple question and this is something that many of you can relate to. How many of you enjoy having a bank account full of money? It’s safe to assume that almost everyone reading this script enjoys having a decent sum of money in their bank account.
I know that there may have been a very, very, very small few that might have said, “Money isn’t real, the real value of you isn’t in the form of numbers.” To them, I ask, if that is true then why is it that every time I get a bill, I spiral into a panic attack? Explain that one, however, you’re not wrong, that’s not the point being made here, so hush.
Suppose like in many situations, you check your account before going to sleep to confirm you have a decent amount, but when waking up you get an alert sounding like the accountant bit from South Park talking about your bank account, “Annnd, it’s gone. Your money, it’s all gone.” Let me script for you how this may have happened.

Photo by Andrea Piacquadio, please support by following @pexel.com
Halloween Gone Mobile
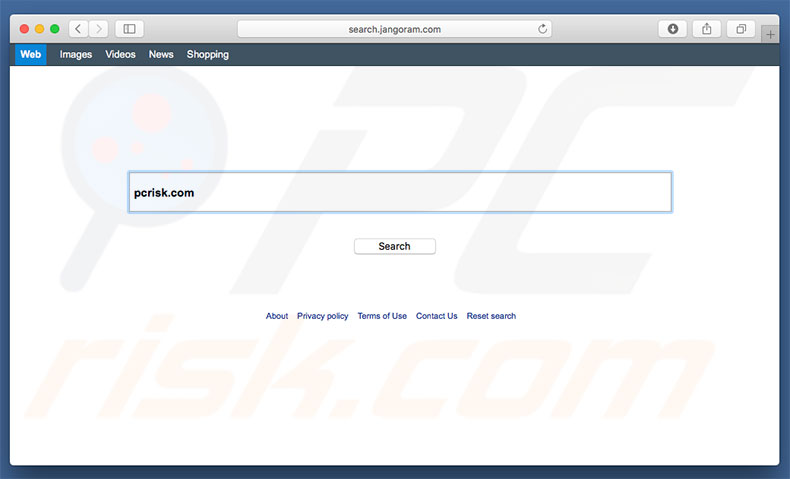
So, the numbers in your bank account are gone with the wind and you’re probably wondering how you got to this junction. Well, let me inform you that you may have been infected with a virus called SOVA.
SOVA is a virus designed for mobile phones, as you can predict this is mainly for Android phones, but iPhone users don’t think you’re safe. Your sweet saucy phone jack is just not on the menu for now.
SOVA, in case you were wondering means owl in Russian, the name was given because owls are nocturnal birds of prey, they’re silent, and like a slow jam from the 80s, they stalk and capture their prey. As you could have already guessed, this is Michael Myers of the animal kingdom, and it very well could be on your mobile device.

Photo by Pixabay, please support by following @pexel.com
Night-time Owls, Day-time Collection
Outside of SOVA being given a cute name by the threat actor, the first version made its first appearance on the underground markets back in September of 2021. For those who don’t know what the underground markets are, they’re the “dark web” or may also be called the “dark net”. And before you ask, no, there is not an underground store in either of those areas.
SOVA was shown that it not only had the ability to collect usernames, passwords, and other information, but it also has an interesting function that will be brought up later. Trust me, you’re not going to like this. If you suffer from having trust issues with people, you’re really going to have it with your phone after reading this script.
Photo by Karolina Grabowska, please support by following @pexel.com
Intruder at Hand
Right now, you’re probably looking at your phone and thinking “I don’t trust you.” And you would be right since your phone is the main attack vector for this malware/virus/trojan. That’s right, viruses have pronouns too.
SOVA is distributed by a smishing attack, which is another form of phishing where the attacker is trying to bait you into clicking on a link for further malicious intent via text messaging.
Once the fake application is installed on the phone, it then sends the list of all applications installed on your device back to the command-and-control server (C2C), this is done with the intent for the attacker to then choose which app to target.
The attacker fires back the malware that can perform collecting keystrokes, steal cookies, intercept multi-factor authentication tokens, copy and paste, and add fake overlays for a range of apps.
But are you ready to have some major trust issues? This malware can perform actions like clicking, swiping, and pretty much interacting the same way as if you were using it. This is all done via the accessibility service, guessing this is the last time you’ll trust a handicap sign.

Photo by energepic.com, please support by following @pexel.com
Panic, Pause, and Simple Steps
While this seems like the sky is falling and you’re never going to dance again because empty words have no rhythm. Though it’s easy to pretend, knowing this information will not make you a fool. Always be very careful when you download from a friend as this could be potential harm that you have been given.
A few other ways of preventing from downloading such malware are to make sure you check all of the details of the application such as reviews and how often the application is downloaded. Make sure you download from only trusted sources like the manufacturer’s store or from the app store.
Other practices are making sure your OS (Operating System), applications, and anti-virus software are up to date. Most of the ways to keep your devices and information safe are to follow simple best practices but most of the time the combination of “It’s our app and we want it now” and reading takes too much effort that exposes us to possible threats.

Photo by John Tekeridis, please support by following @pexel.com
Made it this far and found this to be entertaining? Then a big thanks to you and please show your support by cracking a like, scripting a comment, or plug-in to follow.
Would like to give sincere thanks to current followers and subscribers, your support and actions mean a lot and has a play in the creation of each script.
Do you feel like I may have missed something about SOVA? Script a comment below.