Quick note: if you’re viewing this via email, come to the site for better viewing. Enjoy!

Photo by Matt Hardy, please support by following @pexel.com
Beginning to an End
It has been a rough ride trying to look for a job in Information Technology (IT). All I want is to change careers and improve my quality of living. Is that too much to ask? Pouring countless hours into Bootcamps, completing online courses, and doing code-along projects.
Fixing up my resume to suit resume screening needs. At this point, things have been pretty interesting, to say the least. After months of facing countless piles of rejection, something came through finally.
I finally got my big break, and this was going to be my meal ticket into the big wide world of IT, and with studying areas such as cloud computing, Python programming, and machine learning, it was clear I was on my way to the big leagues. Someone reached out to me and offered me an interview.
My thoughts were, I finally made it past the computer screening. Someone looked at my resume and envisioned the potential.
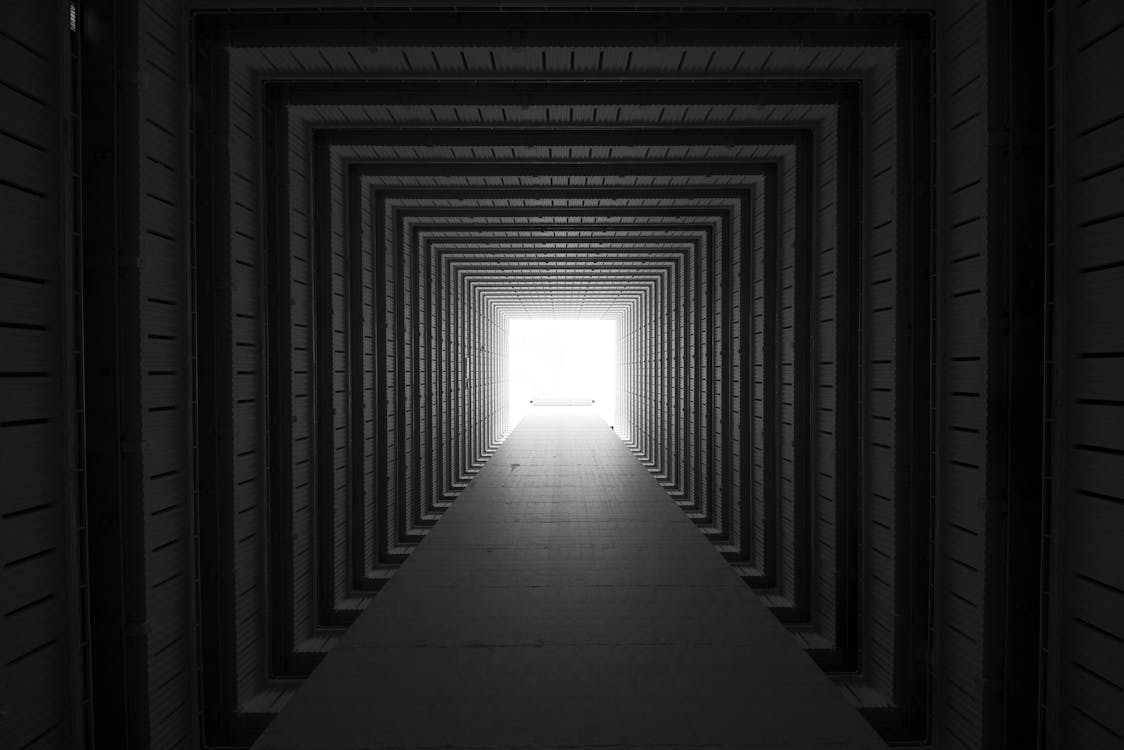
Photo by Xi Xi, please support by following @pexel.com
Moth Set Ablaze
This company wasn’t to the likes of Microsoft, but it wasn’t too small either. I was determined to make this work, even if I stumbled, I was going to give it my all. Like Vin Diesel, I was doing this for “family”.
They gave me a bit of information about their company such as whom they were backed by and what role they are recruiting for. Day came to interview… which was an email by the way. Googled it (it’s a thing) but didn’t think too much of it.
The interviewer was late for the time we agreed to (didn’t think too much of that either), readily filling out this questionnaire. Some questions were easy, others had me trying to figure out how to word my responses.
Whatever the case may be, this was my light at the end of the tunnel, and I wasn’t going to let this slip by since I worked so hard to get here. Tried not to be too in my head. It’s not like I was sitting across from them where I could judge how the question is being asked.

Photo by Andrea Piacquadio, please support by following @pexel.com
Promise with a Dash of Doubt
After filling out the questionnaire and sending it back. I anticipated,” thank you for your interest, despite the fact we are desperately hiring, we decided to go with other candidates”.
However, to my surprise, I received an email the next afternoon congratulating me on the interview and that the board wanted to move forward with my application and grant me the position of application engineer.
I was informed to keep an eye on my email because I would be receiving an offer letter for employment from human resources (HR) to fill out to start my hiring process. My dreams were coming true, and I could finally and wholeheartedly say I was a part of the oh-so-coveted IT world. I could see greatness on the horizon.

Photo by Andrea Piacquaido, please support by following @pexel.com
Beware of The Hand That Feeds You
Later that night, something wasn’t sitting right. I kept reviewing the email that was sent which included that I was going to receive a check via paycheck or electronic deposit that was going to use for purchasing my soon-to-be home office equipment.
This had me promptly questioning with a; “Say what now?” But I quickly dismissed it with an “oh well, I need a job, and if this is going to be my foot in the door. I’ll take it”.
But something still didn’t sit right. I couldn’t just be given a job this quick, and it is a six-figure salary. After scanning the questionnaire several times and viewing there was a street address. I decided to go and see if my having the job was real.
I tracked all my way to this lovely building (which held Microsoft by the way), walked in, knocked on the door, and was greeted by an older fellow who had an AirPod in his ear. I explained my situation and asked if there were any hiring managers around, I could talk to, but before I could get the words out, he replied “It’s a scam, I’m sorry”. My suspicions were correct, how nice.

Photo by Andrea Piacquadio, please support by following @pexel.com
Turning Tables
Instead of feeling sorry for myself, I decided to make the best of my situation. I waited for my offer letter to be sent to me, which I received right as I was being informed this was a scam. I took to LinkedIn to see If I could connect with these people.
However, turn out to be a dead end. The names did not match the faces. I decided to have some fun to offer up some good spirit and email them a proactive email. I sent the one (the interviewer) an email telling them how happy and hopeful I was to get this position and how I couldn’t wait to start working.
That I wanted to know more about him and how well he was connected to the company and the board. Also, I needed the requisition id number since I needed a list of my duties of what was going to be expected of me. And to the other (HR) email informing them that I would not be needing money for the office equipment since I already have the items.
It has been a while now, so I presume they cut their losses.

Photo by Andrea Piacquadio, please support by following @pexel.com
Look Out!
When dealing with a situation like this there is a two-prong attack.
The Interviewer (attacker one)
-Will reach out for a role, you may or may have not applied to. This person will engage and offer an email interview or interview in some form of messaging service.
The hiring manager or human resources manager (attacker two)
-Will send the offer letter and request to purchase office equipment or mini-office equipment.
List of office or mini-office items
- MacBook
- Dual Monitors
- External hard drive/backup system
- Laptop Stand
- A high-quality webcam
- Comfortable desk chair
- Hp LaserJet Pro M15w Printer
- Computer Hardware and Software
- High-Speed Internet Access
- Stress Ball
Made it this far and found this to be entertaining? Then a big thanks to you and please show your support by cracking a like, scripting a comment, or plug-in to follow.
Would like to give sincere thanks to current followers and subscribers, your support and actions mean a lot and has a play in the creation of each script.
Have you ever encountered what could be a scammer?
Script a comment about how you handled the situation.