Consider following on social media!
Quick note: if you’re viewing this via email, come to the site for better viewing. Enjoy!

Photo by RDNE Stock project, please support by following @pexel.com
We as humans, take many things for granted. Family, friends, pets, and quite often, our personal information. We often share our personal data to make purchases or access services, and we expect it will be protected and used responsibly. But how often is this true?
Many organizations sometimes fail to safeguard or even bravely misuse our information for their own purposes. Then go on record saying that it’s a “you problem” and not a “them problem”, which is kinda correct because you didn’t bother to read the twenty-two-page privacy agreement policy.
Word to the wise, start reading those policies. You’ll start to see how jacked-up companies really are. But outside of the evil corporate overlords being okay with you skimming over the fine print, there is a bigger threat to your information, and it happens more than you would think.
Don’t worry, we have you covered on this one. We’re going to be going over what kind of attack this is, who uses it, the functionality and effects upon release, and what are some of the ways you can keep your information safeguarded better than most companies you’ve done business with.

Photo by Andrea Piacquadio, please support by following @pexel.com
The Attack
So, what is this attack that most companies just can’t seem to stop? Well, let’s get you acquainted with what’s called a data breach. For those who might not know, a data breach is a serious incident that can compromise the security and privacy of individuals or organizations.
It occurs when sensitive, protected, or confidential data is accessed, copied, transmitted, viewed, stolen, altered, or used by someone unauthorized. Data breaches can have various causes, such as hacking, phishing, malware, insider threats, human errors, or physical theft.
What’s that? They just take your information, that’s not a big deal we can hear you say. While true however stay tuned because data breaches can result in, but are not limited to, financial losses, reputational damage, legal consequences, or identity theft for the affected parties.

Dude 2: It’s not but phishing is. You might want to change your username, that’s all I’m saying.
Dude 1: Nah, you worry too much. It’ll be fine.
Photo by Wendy Wei, please support by following @pexel.com
Who Can It Be Now
In this crazy world, who would use such a dirty tactic to harm people? The real answer is it could be anyone. There are times when individuals or groups are named but for the most part, a data breach could be on anyone’s part.
One possible suspect, which is a popular case and highly likely in this day and age, is an unhappy employee who may be in the running to leave the company. They might have access to sensitive data and could leak it to competitors or seek to harm the organization.
A few things that could lead up to this would be but are not limited to; sharing passwords with others, the downloading of unauthorized software or applications on company device systems, and networks that can be compromised by negligence, ignorance, or malicious intent. In simpler terms, business owners, if you want to keep your business healthy, try keeping your workers happy.
Always follow the notion that it’s cheaper to keep them. Ah, that good old married life.
Enjoy the read so far? Why don’t you consider subscribing so you can keep up to date?

Photo by Mikhail Nilov, please support by following @pexel.com
That Sinking Feeling
Sometimes, these breaches involve voter information, such as names, addresses, party affiliations, or voting histories. This can pose a serious threat to the privacy and security of voters, as well as the integrity of the electoral process. How does this happen you may wonder.
As mentioned before, data breaches can occur due to various reasons, such as hacking, phishing, insider threats, human error, or natural disasters. Pretty much anything that may be considered critical information that is not authorized access to the individual is a data breach.
So, what could be done with this information? Well, a number of things, none of them good. Your information could be sold, or collected, threat actors could pose as you to others you know in order to trick them into giving sensitive information about you or themselves. The mess of a data breach is limitless, and one should act quickly when compromised.

Photo by Edmond Dantes, please support by following @pexel.com
The Prevention
Not sure if your information was a part of a data breach? Well, we’re here to tell you more than likely it was. As mentioned, all companies are susceptible to their data being leaked.
To prevent or mitigate data breaches, organizations that handle voter information should adopt best practices for data protection because if threat actors have your voter information, then they have your vote. Best practices such as encryption, authentication, backup, and monitoring help to ensure you have a secure connection. you may not always notice the signs of a cyberattack, especially if it targets your social media habits.
For example, you may see a change in the content you view online, such as going from cute animals to political messages. This could be a way of manipulating your opinions or influencing your decisions.
To prevent this, you should regularly check your accounts and settings, and be aware of what you share online. You can also use a website like “HaveIBeenPwned.com” to see if your email or password has been compromised in a data breach.
You can reduce the subconscious effects of these hidden influence strategies by educating yourself. You can watch documentaries like “The Big Hack”, read about how Russia used social media to interfere in Ukraine, the Brexit scandal, and the recent US elections, and learn how social media and voter data are used to manipulate elections.
One way to resist social influence is to be aware of its presence. When you see different people and posts on your Facebook timeline during an election period, don’t assume they are genuine. They might be bots trying to sway your opinion with customized information based on your profile.
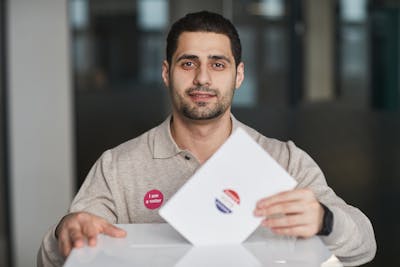
Photo by Edmond Dantes, please support by following @pexel.com
Made it this far and found this to be entertaining? Then a big thanks to you and please show your support by cracking a like, sharing this with whomever, scripting a comment, or plug-in to follow.
Would like to give sincere thanks to current followers and subscribers, your support and actions mean a lot and has a play in the creation of each script.
Do you feel like there is something I may have missed on data breaches? Script a comment below.